“Have you ever heard of a wish sandwich? A wish sandwich is the kind of a sandwich where you have two slices of bread and you, hee hee hee, wish you had some meat…”
These are part of the lyrics from the “Rubber Biscuit” song by “The Chips“, covered by the Blues Brothers in 1978. At the time, UNIX was almost 10 years old, the first version of BSD had been released, and Microsoft had their office in Albuquerque with Bill Gates being 23 years old.
It would take almost another 20 years before Windows NT 4 would be released. But back to the future now.
Well, after working with Windows for about 15 years now, I also wish that the base set of utilities that ship as part of Windows would have been updated and improved. It might seem odd, but one of the first things I do when I install a new release of Windows, is to open notepad, the calculator and paint – to see if they have improved.
Somewhat surprisingly, Windows 7 brings a lot of improvements to the core utilities that ship with Windows. Microsoft not only spiced up Paint and Wordpad by giving them the “Ribbon”, but also improved the calculator in ways never imagined before. Yeah!
 But these improvements do not satisfy a long-time Windows user! Having worked with Linux, OS X and Windows since the 3.0 days, I have my own list of apps that I use to substitute or extend some of the archaic tools that ship with Windows.
But these improvements do not satisfy a long-time Windows user! Having worked with Linux, OS X and Windows since the 3.0 days, I have my own list of apps that I use to substitute or extend some of the archaic tools that ship with Windows.
And here they are:
1. Notepad
What we know today as “Notepad”, was first seen in Windows NT 4.0. When Windows 2000 came out, notepad hadn’t changed. Well, fair enough – it had only been 4 years after all. A short while later Windows XP was released with a bang, but notepad was still the same. Windows 2003 showed that an upgrade to notepad obviously had low priority, and the release of Vista confirmed to me that notepad was clearly no longer under development. The recent release of Windows 7 crushed my hopes of Microsoft ever releasing an updated version of Notepad. Sigh.
So, why was Notepad left behind? Well, I have a few theories:
a) The developer who originally developed Notepad has left the company, and nobody at Microsoft understands the existing code enough to make modifications.
b) Companies developing third-party editors formed a powerful, mafia-like lobby, threatening Microsoft (presumably kidnappings) to never ever release an update to notepad, to ensure that third-party editors will continue to sell well.
c) Microsoft deems Notepad complete, and cannot imagine how this robust application could be improved.
d) Windows applications do not use text files, since all configuration is stored in the registry or databases. Even though unneeded, Notepad is provided as a courtesy and might be excluded from future version (like, telnet.exe!).
 Whatever the reason (I may never find out), fact is that Notepad hasn’t been updated in 13 years, and since Windows 8 won’t be out until 2012, probably won’t change in 16 years. That’s a lot of years for a software program.
Whatever the reason (I may never find out), fact is that Notepad hasn’t been updated in 13 years, and since Windows 8 won’t be out until 2012, probably won’t change in 16 years. That’s a lot of years for a software program.
Line Numbers?
Basic syntax highlighting?
Anyone?
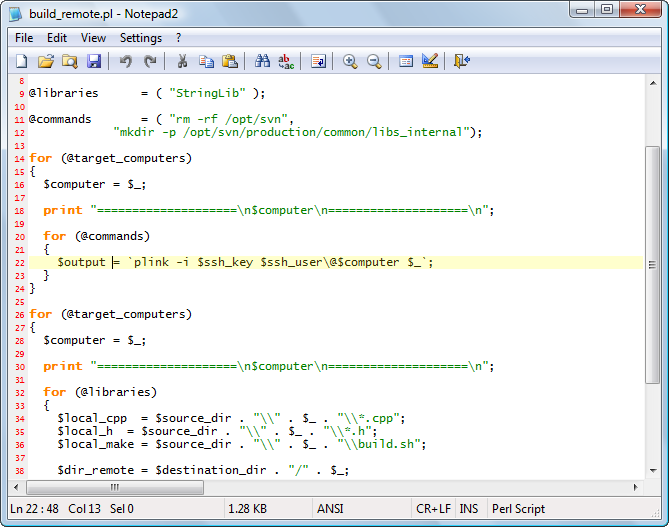
So what could replace Notepad? Why, Notepad2 of course! To be fair, there are more powerful editors out there than Notepad2, but it’s free, light-weight and fast. Florian’s Notepad2 supports line numbers, syntax highlighting, line highlighting, encodings, Unix/Windows line endings, transparency and much more. An extended version from Kai Liu is also available here, most notably including code folding abilities. Tabs are not supported in either version, unfortunately.
My other favorite editor is Ultraedit, as it includes pretty much any feature you could ever want from an editor. A nice feature, for sysadmins in particular, is the ability to switch environments. The “System Administrator” view for example, allows you to show SSH/telnet/FTP windows along with the editor windows.
2. Command Prompt
Yeah, this hasn’t changed much since the early days either, though the introduction of the PowerShell deserves some credit. Using Linux regularly though, I miss some of the features like tabs, transparency and so forth.
 The good news is, there is an excellent substitution out there called Console. The latest beta of version 2 features transparency, multiple tabs, appearance options and is free. It’s so free, that they even give you the source code if you want it! It works on all the machines I use (mostly Vista, soon to be Win7) and I’m very happy with it overall – though it is a beta still and you might run into a glitch every now and then. I sit around in the command line a lot, and having multiple tabs open is nice.
The good news is, there is an excellent substitution out there called Console. The latest beta of version 2 features transparency, multiple tabs, appearance options and is free. It’s so free, that they even give you the source code if you want it! It works on all the machines I use (mostly Vista, soon to be Win7) and I’m very happy with it overall – though it is a beta still and you might run into a glitch every now and then. I sit around in the command line a lot, and having multiple tabs open is nice.
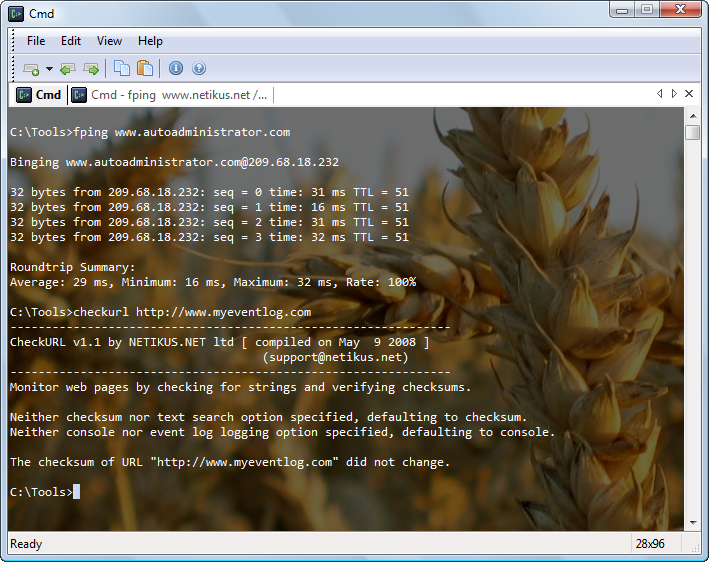
One option I really like is the ability to show the currently executing command as the tab title, which is useful because you can see when a long-running process finishes (see screenshot above where fping is running in the 2nd tab).
When downloading, get the latest beta and simply extract all files from the
Console2\bin\release
folder to a directory of your choice.
3. Desktops / Spaces
Linux, and Unix, had multiple desktops since the industrial revolution. Well, at least it seems that way. I’m not sure why this hasn’t been added to Windows yet, given that:
• Every major Operating System OTHER than Windows includes it
• Microsoft provides a tool (part of Sysinternals) that offers this functionality
Yes, in the age of affordable large monitors, multiple desktops aren’t really that necessary anymore. But, many of us still work on laptops and having multiple virtual desktops can help group different work into different workspaces.
I recommend Sysinternals’ Desktops, but there are more tools out there that do the same thing – though they are not all free.
 4. Launchy
4. Launchy
It indexes all of your applications in the start menu, and you can simply launch them by typing their name – or part of their name. No
longer do you have to wade through dozens and dozens of menu items just to find a shortcut. Simply launch Launchy with ALT+SPACE and type a couple of letters. Voila!
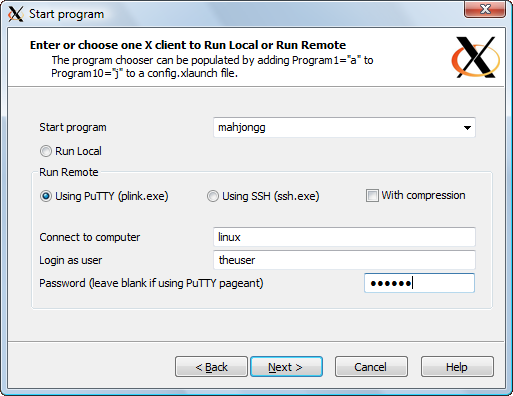
 5. PuTTY
5. PuTTY
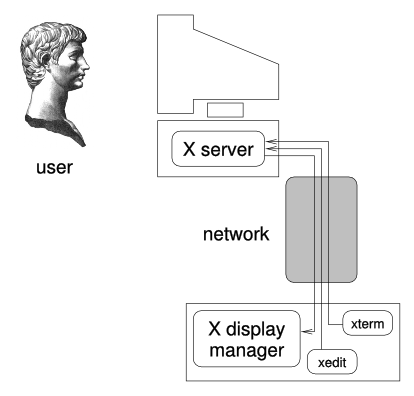
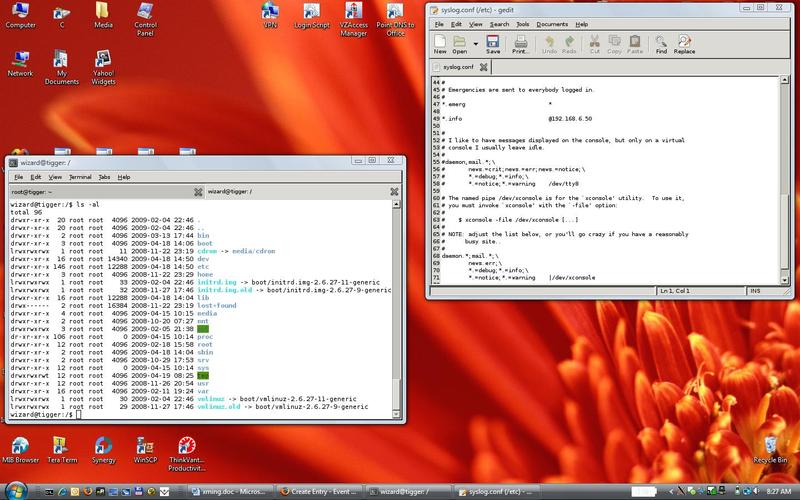
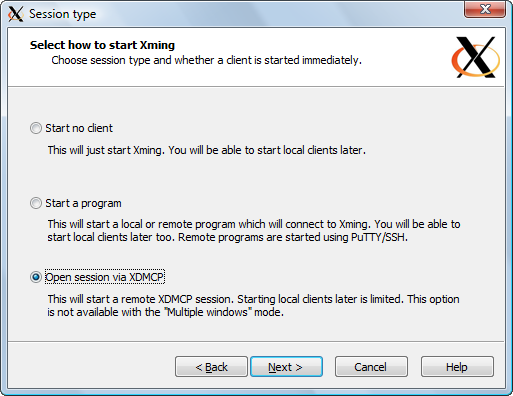
If you work with Windows and UNIX/Linux machines, then it’s pretty much impossible that you haven’t heard of PuTTY. It’s a free SSH client that no only provides SSH/Telnet functionality, but also comes with other SSH-related utilities like PSCP, PSFTP and PLINK (see previous post on this).
I’d love it if Windows would ship with a command-line SSH client, just like all UNIX and Linux distributions do.
Of course there is more, but these are the tools “desktop” that we really use on a daily basis.
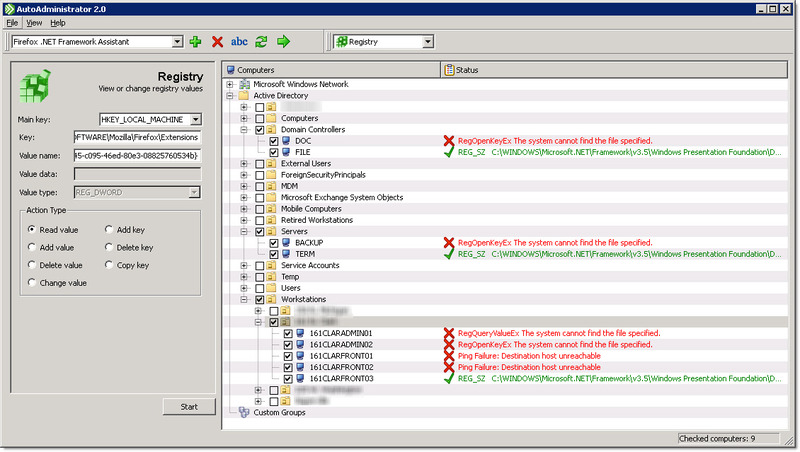
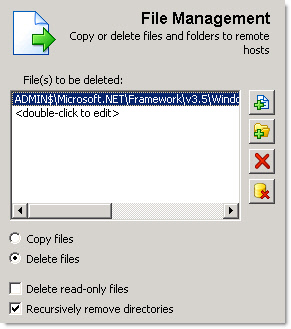
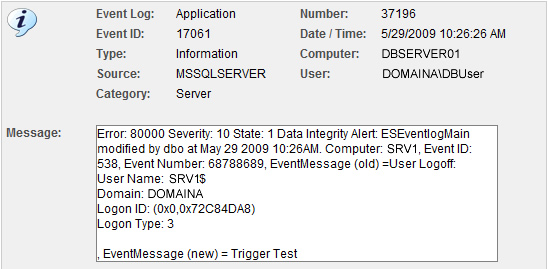
If your computers are in an Active Directory domain and you want to roll out some of these tools with your computers by default, then I recommend reading our previous post: Your favorite tools and utilities always available everywhere.
What do you want for nothing?
Rubber Biscuit?